Trezor Bridge: Secure Connection for Your Crypto Wallet

Introduction to Trezor Bridge
Managing cryptocurrency safely requires reliable tools that protect your assets from online threats. One such essential component is Trezor Bridge, a small but powerful piece of software that connects your hardware wallet to your computer browser or application. It acts as a secure communication layer between your device and compatible wallet interfaces.
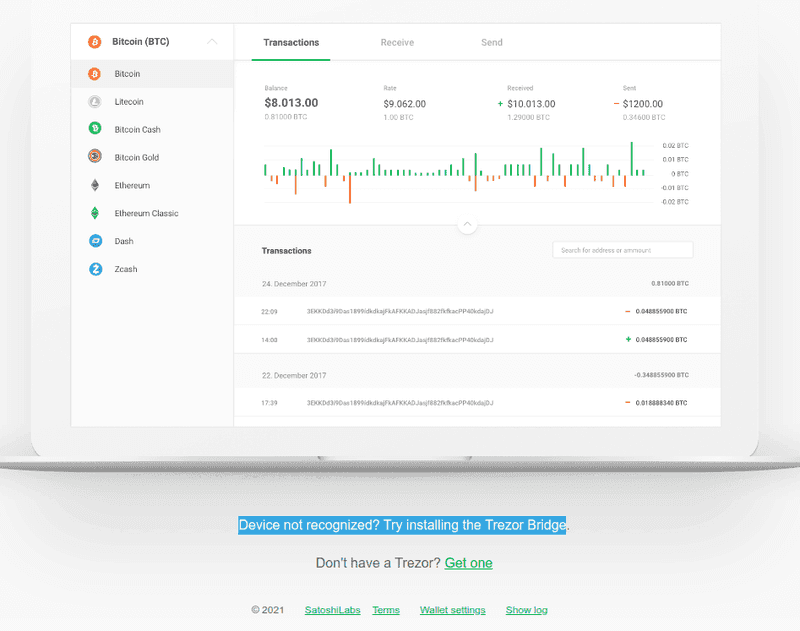
Developed by SatoshiLabs, the bridge ensures that your hardware wallet communicates safely with supported platforms like Trezor Suite or web-based wallet services. By installing this tool, users gain a seamless and secure connection for managing digital assets such as Bitcoin and many other supported coins.
This article explains how Trezor Bridge works, its benefits, security features, and why it plays an important role in protecting your cryptocurrency.
What Is Trezor Bridge?
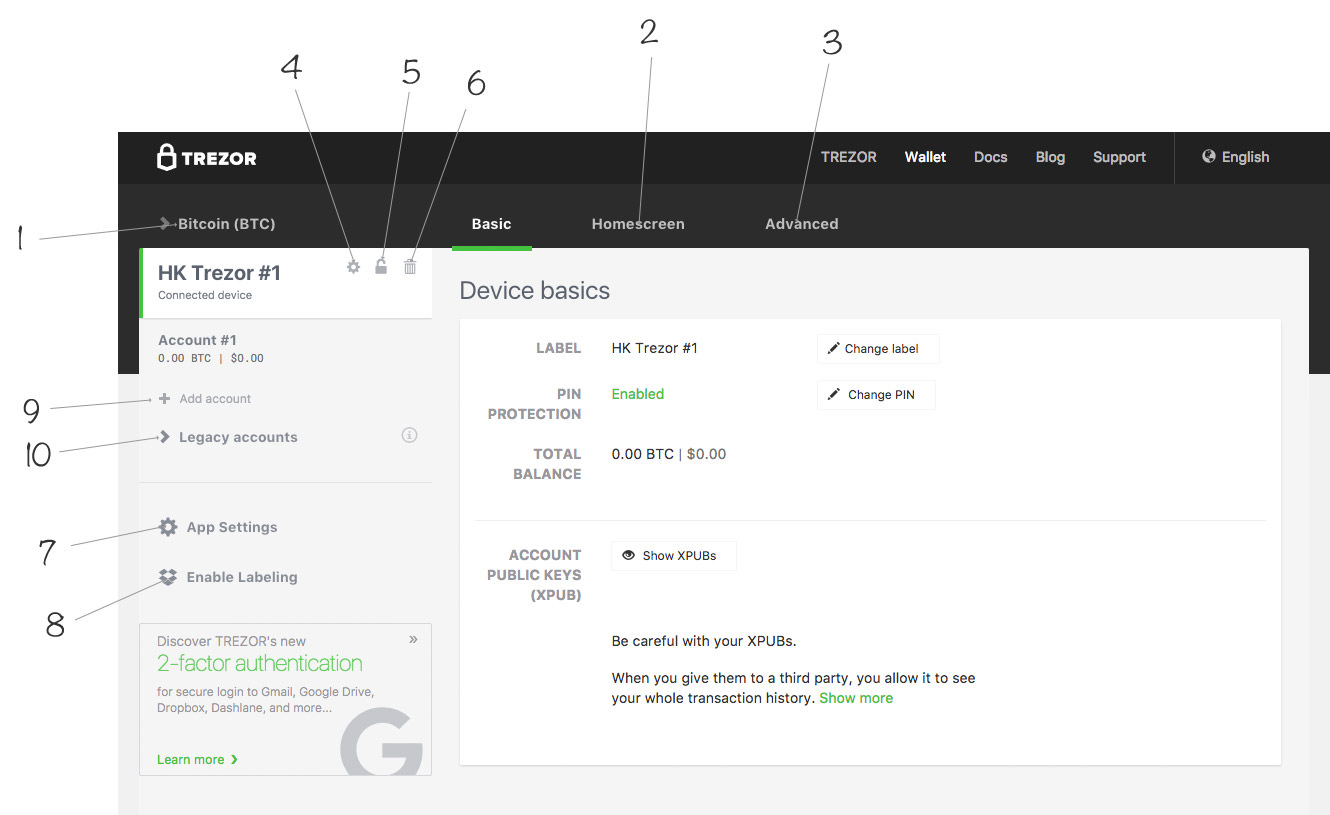
Trezor Bridge is a lightweight background application that enables communication between your hardware wallet and your browser or desktop wallet interface. Many modern browsers restrict direct access to USB devices for security reasons. The bridge solves this limitation by acting as a safe intermediary. ([Google Sites][1])
In simple terms, the process works like this:
Browser or wallet app → Trezor Bridge → Trezor device
The bridge receives requests from the wallet interface and securely passes them to the connected hardware wallet through encrypted communication channels. ([bridge-tezorfaq.pages.dev][2])
Once installed, it runs quietly in the background and automatically detects your device when connected.
Key Benefits of Trezor Bridge
1. Secure Communication
Trezor Bridge encrypts communication between your computer and hardware wallet. This ensures that transaction requests and commands cannot be intercepted or manipulated by malicious software. ([trezore-bridge.framer.ai][3])
2. Private Keys Stay Offline
One of the most important security features is that private keys never leave the hardware wallet. The bridge only transfers transaction data, while signing happens inside the device itself. ([Trezor Bridge][4])
3. Cross-Platform Compatibility
Trezor Bridge works smoothly across major operating systems including:
- Windows
- macOS
- Linux
This ensures consistent connectivity regardless of your preferred device environment.
4. Seamless Background Operation
After installation, the bridge runs automatically and detects the connected hardware wallet. Users do not need to configure additional settings, making the experience simple and user-friendly.
5. Protection Against Phishing
Since all transactions require confirmation on the hardware device screen, attackers cannot authorize transfers without your physical approval.
How Trezor Bridge Enhances Security
Security is the foundation of Trezor’s ecosystem. The bridge plays a critical role by adding multiple layers of protection.
Local Communication Only The software communicates only through the local system environment, preventing external servers from accessing wallet commands. ([brrdge-en.framer.media][5])
Origin Verification It verifies the source of requests to ensure that only trusted applications can interact with the hardware wallet.
Encrypted Data Transfer All transaction data and communication between the wallet interface and device are encrypted, protecting users from interception or tampering.
These mechanisms ensure that even if a computer is compromised, attackers cannot steal funds without confirmation on the hardware device.
How to Install Trezor Bridge
Installing Trezor Bridge is straightforward and takes only a few minutes.
- Visit the official Trezor setup page.
- Download the latest version of the bridge for your operating system.
- Run the installer and complete the setup.
- Connect your hardware wallet to your computer using USB.
- Open the wallet interface to start managing your crypto assets.
Once installed, the software automatically runs in the background whenever your system starts.
Why Trezor Bridge Is Important for Crypto Security
Hardware wallets are considered one of the safest ways to store cryptocurrency. However, secure communication between the device and the computer is equally important.
Trezor Bridge ensures this connection remains encrypted, verified, and protected from unauthorized access. By acting as a secure gateway, it allows users to interact with their wallets confidently while maintaining the highest level of privacy and security.
For anyone using a Trezor hardware wallet, installing the bridge ensures smoother connectivity and stronger protection against online threats.
Frequently Asked Questions (FAQs)
1. What is Trezor Bridge used for?
Trezor Bridge is used to connect your Trezor hardware wallet with your computer browser or wallet application, allowing secure communication between the two.
2. Is Trezor Bridge safe?
Yes. The software uses encrypted communication and keeps private keys inside the hardware wallet, ensuring that sensitive data never leaves the device.
3. Do I always need Trezor Bridge?
It is required when using certain browsers or web interfaces that cannot directly communicate with USB hardware wallets.
4. Does Trezor Bridge store my private keys?
No. Private keys remain stored in the hardware wallet. The bridge only transfers signed transaction data.
5. Which operating systems support Trezor Bridge?
Trezor Bridge supports Windows, macOS, and Linux systems.
✅ Conclusion: Trezor Bridge plays a vital role in enabling secure communication between your hardware wallet and wallet interfaces. With encrypted communication, device-side signing, and strong privacy protections, it helps ensure that your cryptocurrency remains safe while giving you a smooth and reliable user experience.